Do you want to know what’s common between WhatsApp, Facebook, and Fortnite? Apart from the fact that at least one of them is a part of our Smartphones, Tablets, and PCs, they also share a common piece of bad news for their users.
There’s no point denying that similar issues like data theft, hacking, fraudsters, and scammers hide deep inside the roots of the internet.
And will be increasing faster than ever, and that too at an alarming pace. According to idtheftcenter, there were 425,078,513 victims of cybercrime in 2022 and global cybersecurity crime damage is expected to reach $15.63 trillion by 2029.
Best Tips To Secure Your Devices
Here in this article we have listed the best tips to secure your devices in 2026.
1. Downloading from unknown sources
Every Operating System has its own application store from where you can download applications. Most people download and install applications from their browsers that aren’t found on their device’s store.
It seems fun until you know the repercussions. Since developers don’t have to go through malware checks on browsers, they can upload any kind of virus or spyware that they can. Downloading such applications would only make you a sucker of these loopholes.
2. Enable A Firewall
While not being of any big use for individuals, firewalls are of utmost importance to corporations and individual employees that use private networks like intranet instead of the internet.
A firewall is a system that blocks any unauthorized access from a public network to a private network. Since hackers generally try to interfere with corporate networks, small businesses are deemed to invest in security systems, especially firewalls.
3. Use A Virtual Private Network (VPN)
A VPN is a network that helps us to connect to another network securely without the interference of a third party including private organizations and even the government.
It was initially used by businesses to establish a secure connection over the internet, but nowadays individuals like us use VPNs to anonymously browse the web without being tracked, watch media restricted in their own country and prevent their server address and geolocation to be tracked.
4. Give Your Account Details to Trustworthy Websites Only
Internet is a network of millions of websites and most of them ask to sign up for their newsletters, create accounts with email, names, and phone numbers. Logging in and creating accounts into unknown websites that don’t have any privacy policy can land your data into trouble.
Always check the authority of a website, applications, or any other service that asks you to sign up in return for service.
If your bank account details are being asked for making the payments, look if the payment gateway is encrypted and trustworthy or not. Leakage of bank accounts leads to numerous financial frauds worldwide.
5. Install and Enable an Adblocker
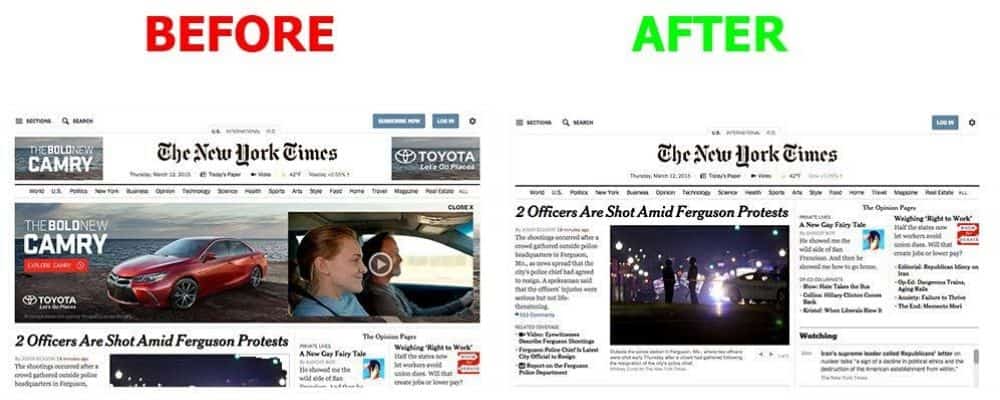
You’re not the only person who surfs the web and hates online ads. Millions of users feel the same about ads. Other than being irrelevant to the content you’re looking for; ads also help Cybercriminals post malicious content on respectable websites as well as track your data and use it against you.
An Adblocker is a software or an add-on to a browser that replaces all kinds of ads with white space, which is how they were originally supposed to look like.
6. Be Cautious While Surfing Websites Without SSL Certificate
An SSL certificate is a combination of files installed on a web server that secures the connection between that server and the browser of the user. In simpler terms, it is a set of documents that secure all the activities carried out between a user and a website on the internet.
Websites with SSL certificates either show a “padlock” symbol beside the URL in some browsers or their URL begins with “HTTPS” instead of “HTTP”. Websites without an SSL certificate are more prone to cybersecurity leaks. Think twice before submitting your critical data to such websites.
7. Create A Cloud Backup of Your Files

A cloud backup is a strategy that uses and infrastructure of powerful, secure computers on which you can upload, modify and edit your files through the internet.
Creating cloud backups of important files not only creates a copy but also creates an option in case those files get corrupted, lost or destroyed, which happens a lot of time. You also get free extra space on several platforms which makes this process free of cost for individuals.
8. Never Get Yourself Landed on the Dark Web
The deep web is 99% of the internet and has a network of websites that can’t be identified at all using normal browsers. It may seem intriguing for the curious mind at first, but the dark web is for illegal activities, most of them include data, drugs, weapons stolen being sold.
But rumors have it that apart from landing you in jail, the dark web can create an opportunity for experienced hackers to steal and access the location and server address of inexperienced, innocent people who just came there for fun.
9. Don’t Connect to Unauthorised Free WIFI’s
Free Wi-Fi with powerful speed and that too at a public space is a “want” right? Well, maybe not. At least if its source isn’t an authority. For instance, free Wi-Fi at museums provided by the government itself is the internet that can be trusted and connected to.
But if you were to ever see your laptop/smartphone receive Wi-Fi signals having either a fishy name or pertaining to a source that shouldn’t be there, it would be a good indicator to not connect.
Technology has made it easy for hackers to control your devices and enter into your private data just through your permission to get yourself connected to their ‘free-Wi-Fi’.
10. Install and Enable Find-my-device
Smartphones, tablets and laptops get stolen and lost so frequently that you are very likely to face a device theft at least twice in your lifetime.
Luckily, you can easily find your device if it either gets lost, or someone finds it and cannot return it somehow, or it gets stolen by a careless thief, by using find my device (for android and windows) or find my mac/iPhone (for IOS users).
Preinstalling any of these applications can save you your precious money and data instead of starting it all over with a new device.
11. Use Trustworthy Applications and Software
We use multiple applications and software daily. The app stores provided by our Operating Systems sometimes overlook and put applications made by irrelevant and shady manufacturers in their index.
Downloading such apps and submitting your accounts into their databases is a sure-shot way to see your data manipulate, or worse, hacked soon.
12. Read Terms and Conditions Thoroughly
Anything we software we from the web (be it on a Mac, Windows, iPhone and Android) shows us its terms and conditions, that includes the company policies and especially what is it going to do with all the inputs and activities you carry out in that application.
Even if you ignore most of the terms and conditions part, make sure you read about their privacy policy.
Fun Fact: Many software companies get the right to use your data, sell it and modify it through the consent you give by clicking “I agree”.
13. Install A Security Package/ Antimalware
Anti-Malware protects users from hacking, system corruption, explicit adware, worms, and whatnot. But it’s always better to invest in reliable and paid antimalware since they provide functions such as theft insurance as well.
The in-app protection can help in making all the applications highly secure from all the malware and other attacks.
14. Use Highly Secure Passwords
As technology has brought in Touch ID and Face ID into smartphones, they have become the most popular making passwords and pins the least used methods of securing a smartphone.
These IDs have many security issues, the prime one being that they can be cracked easily. Touch ID just needs your fingerprint which can be tapped on by anyone even if you’re sleeping. It is much safer to use a password or a pin.
15. Password Protect Your E-documents
Most government and private organizations accept e-documents like certificates, Bio-data, and ID proofs these days, which is why we like to keep them safe in our laptops and desktops.
Some organizations even encrypt the documents themselves before sending them to us. Even if they don’t, it is a responsibility of us to encrypt any document that contains our details.
16. Keep Your Operating Systems Up-to-date
Security bug fixes are an important part of OS updates, apart from performance enhancement, of course. Security bugs are the loopholes for cybercriminals to act upon, which is why you should always keep your smartphones and laptops up to date, be it IOS, Windows, Android, or Mac.
A better option is to permanently put the OS on ‘Automatic Update’ to relieve yourself from doing it by yourself.
17. Run Malware Scans Regularly
Malware isn’t something that starts to create problems as soon as it enters your device. Most of the times things such as Trojans, viruses and spyware try their best to remain hidden until the right time.
Which is why it is better to run system scans regularly using an antivirus. Most antiviruses offer an option between full system scans and overall scans depending on the time you can spend on scanning.
As a rule of thumb, you should scan for viruses as soon as the system starts acting weird.
18. Hard Drive Encryption
The best way to secure offline data to prevent it from being stolen is Hard drive encryption. Hackers can retrieve your hard drive even if your PC/Laptop has a strong password. It simply takes some know-how and your hard drive, be it SSD or HDD.
To prevent your data from being leaked online, software such as BitLocker (Windows) or FileVault (Mac). can help you. This way, if anyone wants to access your hard drive, they would only be able to do so with a password. Without the password, data retrieval is nearly impossible which makes your media secure than ever.
19. Identify Fraud Calls
Phone frauds began scamming people decades ago and sadly, still exist. Lack of education isn’t the main cause of the success of phone scams.
It is the conditions that the scammers put ahead of victims by knowing their details and posing as authoritative and concerned personnel that make us suckers to such frauds.
The best way to identify a phone scam is by questioning. Even if you think that you’re talking to the right person, you should ask for credentials and make sure that you’re giving your details after being sure of their identity.
20. Scan External Devices Before Connecting
Internet isn’t the only way for cybercriminals to threaten your device security. When you connect a peripheral like a USB, hard drive or OTG (in the case of smartphones) for data transmission, your device also receives viruses and Trojans inside those external devices.
These Trojans and viruses can enter into your gadgets without permission, which is why you should always scan any external connection before transmitting data.
Conclusion:
In 2026, securing your devices involves using strong passwords, enabling two-factor authentication, keeping software updated, and encrypting communications.
Stay alert to phishing, back up data regularly, and use trusted security tools to protect against threats. Staying informed ensures long-term digital safety.
Also Read:


1 comment
Wow! What a great an extensive guide! I have tried some of the tips you recommended. Definitely going to try using a web adblocker!