Understanding OWASP
OWASP Is the acronym for Open Web Security Application Project. It is a non-profitable organization that aims to enhance the security of any software as a web application. This organization publishes a list of web security vulnerabilities based on the data collected from various organizations.
OWASP top web vulnerabilities are further prioritized based on parameters like- exploitability, detectability and their impact on the web applications.
So, how exactly are these parameters defined by OWASP?
1) Exploitability
Exploitability can be seen as the factors that are needed for exploiting a web security vulnerability. The highest degree of exploitability takes place solely with a web browser. On the other hand, the least exploitable ones are confined to advanced programming and tools only.
2) Detectability
Detectability can be defined as the extent to which the vulnerability was easily detected. The highest detection degree lies with the information being displayed on the URL or some form of Error Message with the lowest one being the source code.
3) Impact/Damage
Impact or damage of vulnerability can be seen as the extent to which harm might be possibly carried out by a web vulnerability in case it gets attacked. The highest degree of impact/damage of vulnerability can lead to an entire crash of the system. On the contrary, the lowest degree could possibly have no effect.
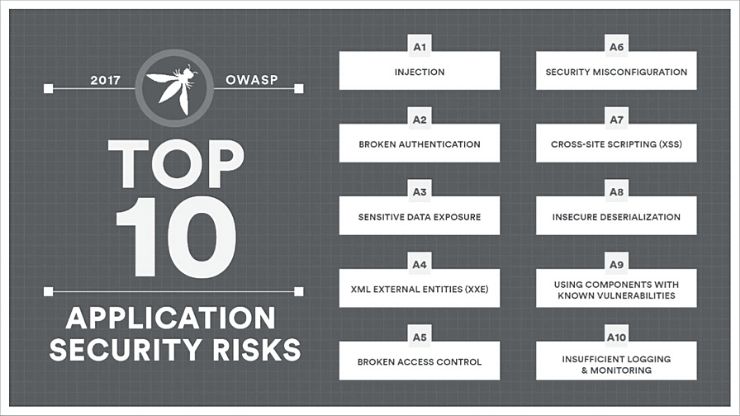
One of the primary reasons why OWASP publishes Top-10 Vulnerabilities is to educate everyone involved with web security about the most significant web vulnerabilities. The latest list of OWASP vulnerabilities was published in 2017.
OWASP Top 10 Vulnerabilities
Following are the list of latest OWASP Top-10 Vulnerabilities that were published in 2017 by the OWASP. Also, this section discusses the implications that each of these vulnerabilities can have on web security or applications.
1) SQL Injection

SQL Injections are a web vulnerability by which the cyber attacker can alter or modify the SQL statements at the backend based on the data provided by the user.
This vulnerability takes place when user input is sent to an interpreter as a part of either command or query. The attacker also fools the interpreter to run the wrong commands for gaining access to any unauthorized data. The wrong SQL command, when executed by a web application exposes the database present at the backend.
Implications:
SQL Injection can have implications like- the attacker injecting malicious content in the most vulnerable fields of the database. Sensitive data of the user can also be easily read from the database.
Further, there is a risk that the database can be modified as per the attacker’s wish. Also, the admin-related operations can be carried out on the database.
Also Read: What is Zero-Day Attack? How to avoid it
2) Cross-Site Scripting

Cross-site scripting or XSS vulnerabilities target the embedded scripts on a webpage that gets executed on the client-side. This type of vulnerability takes place when the application unauthenticated data is taken and sent to the web browser without any validation.
Cyber attackers deploy this vulnerability for executing malicious scripts on the users’ web browsers. As the browser can’t determine the malicious script, thus it can be performed with the attacker taking over the session cookies and redirecting the user to a malicious website.
Implications:
The attackers can deploy this vulnerability by injecting malicious scripts, get away with the session cookies and execute the malware on the victim’s website.
3) Broken Authentication and Session Management

Whenever a user visits a website, it tends to create a session cookie along with a session ID for every valid session. These cookies hold critical sensitive information of the user.
Whenever a session is terminated, these cookies should be invalidated. In case these cookies are not overridden, then the stored sensitive data continues to be present in the system.
In case any user is using a public system and closes it abruptly. There is a high possibility that the attacker might also be using the same system, leading to the compromise of sensitive data.
Implications:
The cyber attacker can encash on this vulnerability for overtaking a user session and gaining unauthorized access to the system. Sessions can also be hijacked with the help of cookies using the XSS vulnerability.
Also Read: What are Google Warning Messages
4) Insecure Direct Object References
This type of vulnerability takes place when a developer references an internally implementable object like- a file, directory or a database key. Any cyber attacker can leverage this information to gain access to other objects by creating a future attack plan for accessing any unauthorized data.
Implications:
Using this vulnerability attack, the attacker gains illegal access to unauthorized internal objects, and thus he can modify the data as per his needs. There are chances that the attacker might even compromise the web application.
5) CSRF

CSRF is the acronym for Cross-Site Request Forgery. This vulnerability attack occurs whenever any malicious website or email causes the user’s browser to carry out a wrong action on a trusted site.
In the CSRF attack, it forces the victim to send an HTTP request to a vulnerable web application with the victim’s cookie along with any authentication information.
Here, the attacker shares a malicious link with the victim. After the user has opened the shared link, data gets stolen from the user logged-in website.
Implications:
Attackers can use this vulnerability to change the user profile information of the user. The attacker can also create a new user on behalf of the admin.
6) Security Misconfigurations

Security configurations need to be clearly defined and deployed for various applications, frameworks, servers and other online platforms. In case of poorly set up settings, it can lead to attackers having unauthorized access towards sensitive data.
Such loopholes in the security configuration need to be taken care of so that there is no system compromise. Also, one should have the latest software in web applications as a robust security mechanism.
Implications:
By taking the due advantage of poorly configured security, the attacker can list out the underlying technology along with server and database information regarding the application for newer attacks.
Also Read: Tips to Secure your Devices in 2020
7) Insecure Cryptographic Storage

It is a common form of vulnerability that exists whenever sensitive data has not been securely stored. The data is going to present in the application database and when such information is not encrypted, it becomes easier for the hackers to exploit it.
Implications:
Using this vulnerability attack, the attacker can get away with the weakly secured data for carrying out theft and fraudulent crimes. The attacker might even modify the less secured data as per his needs.
8) Failure to Restrict URL Access

Web applications often validate the URL access rights before rendering the protected links and buttons. The web apps also need to carry out similar access control checks whenever such pages are accessed.
Most of the applications, privileged pages along and resources are not usually shared with authorized users. An attacker sometimes gains access to such privilege pages and view the confidential information of a user.
Implications:
The attackers can exploit this vulnerability for gaining illegal access to all such unauthorized URLs, without even being present in the application.
9) Lack of Transport Layer Protection

This vulnerability attack is concerned with the information that is being exchanged between the user and the server. Web applications send out sensitive information regularly, such as user authentication details, bank details over networks.
When the websites deploy weak algorithms or expired SSL certificates, it can lead to the exposed communication of the users, ultimately leading to the compromise of a web application or stealing away any crucial information.
Implications:
Using this vulnerability, the attacker can get away with the authorized user’s credentials to gain access to the applications. Since there are no robust security mechanisms in place, attackers can get away with vital information.
Also Read: What is Silex Malware
10) Invalidated Redirects & Forwards

Traditionally, web applications deploy certain methods for redirecting the site users to other pages with an intended purpose. In the absence of the right validation, the attackers can redirect users to other pages using phishing sites, emails.
Implications:
The website user can be easily fooled as an attacker can send the URL to the user containing a genuine URL replaced by a malicious link.
Concluding Remarks
Any web application or website user must be aware of all the web vulnerabilities that might occur. OWASP servers as a parent body by assisting the users against top vulnerabilities time and again.
Once these vulnerabilities have been identified, the web users must ensure that they deploy a trusted web security scanning tool like Vtmscan which can audit digital assets against such threats and vulnerabilities.

